14 January 2021
Request your demo of the Sigrid® | Software Assurance Platform:
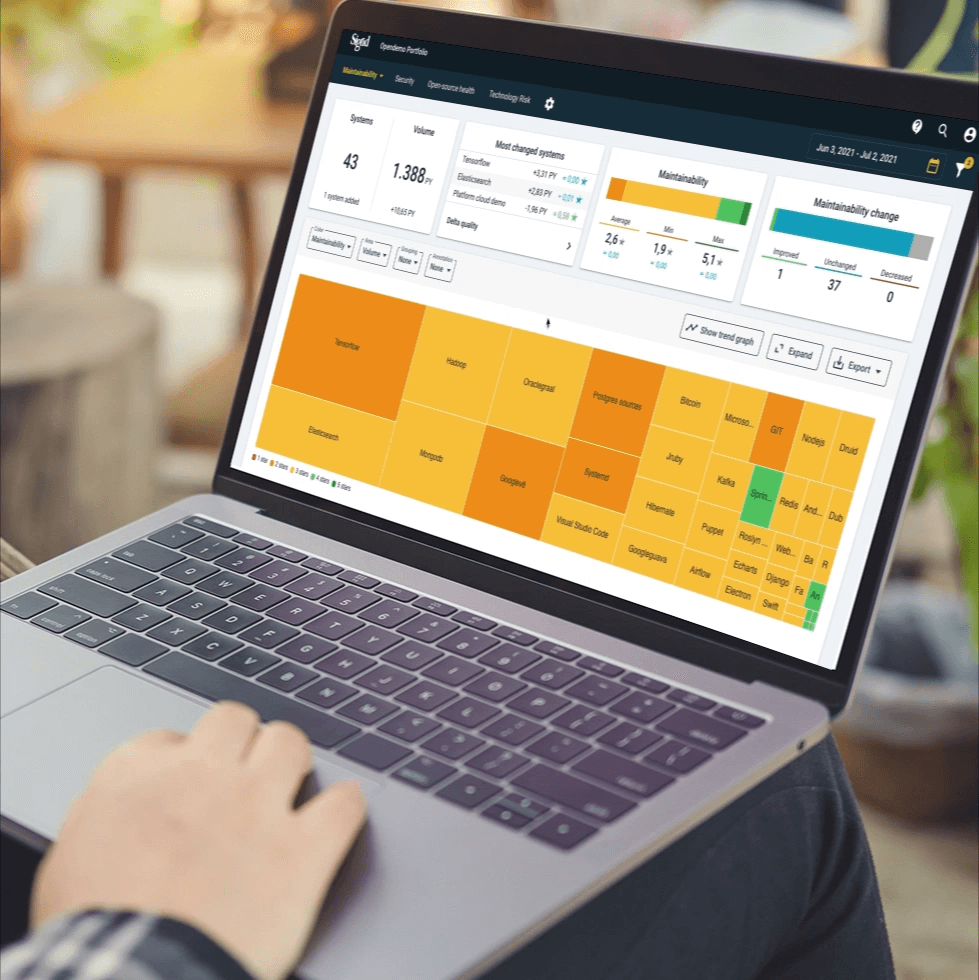

Your legacy IT is likely riddled with security vulnerabilities.
Sorry about that. Good news is our software experts are solving for this every day.
Sorry about that. Good news is our software experts are solving for this every day.
To get you started assessing your own vulnerabilities, Theordoor Scholte, PhD authored this guide, which highlights the three most typical causes of security issues in legacy IT systems:
Lack of security by design
Dependencies on old and insecure components
Immature development process
Even better, he outlines your top three actions to improve your security posture.
Take the advice in this guide before your old legacy software can create a new crisis for your organization.