Legacy Modernization Assurance
We qualify your software landscape architecture, create your risk-based modernization roadmap to ensure your software is fit for business purposes.
Let’s Talk+2B

lines of code analyzed weekly
source of truth

Risk-based scenario's
Choose the data-driven path to legacy modernization
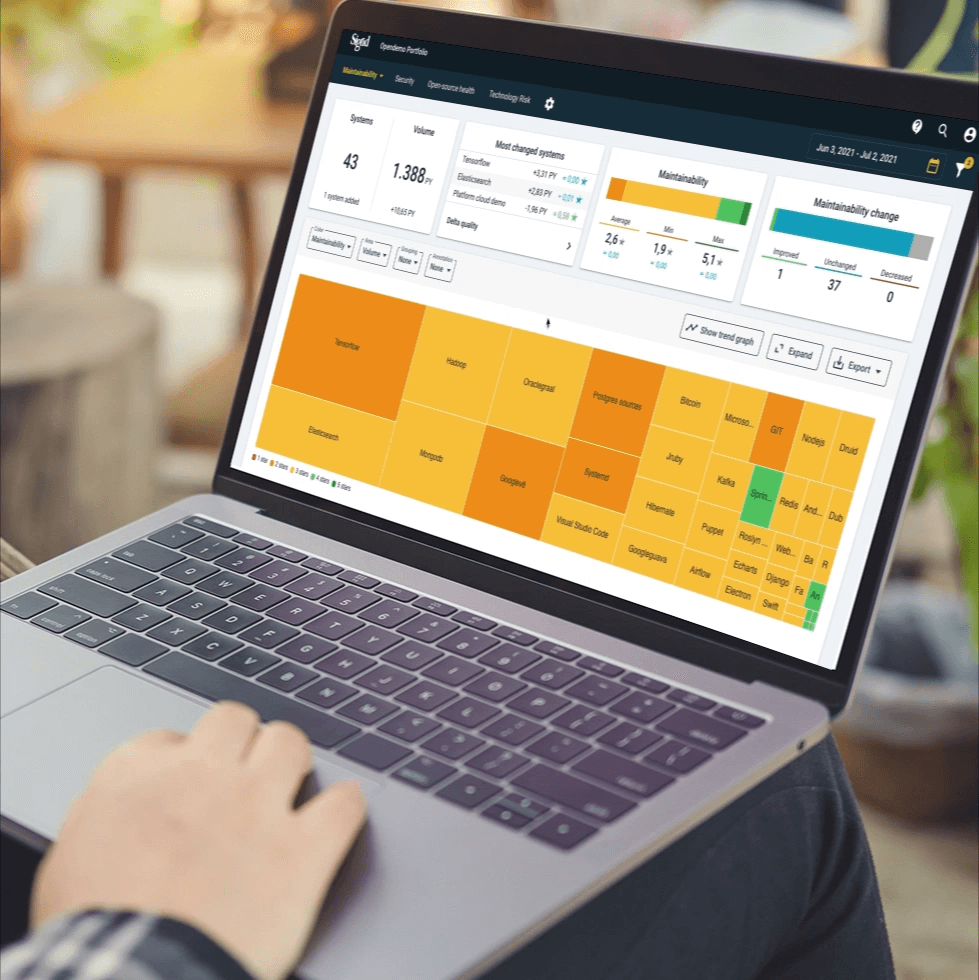
SIG Legacy Modernization Assurance takes a fact-first approach to assess architectural composition, current system build quality, data stores and active knowledge of development teams.
Powered by our proprietary architecture quality model, SIG assures modernization for landscapes of any size, breaking down complex legacy architectures and translating these facts into risk-based scenarios for modernization.
Powered by our proprietary architecture quality model, SIG assures modernization for landscapes of any size, breaking down complex legacy architectures and translating these facts into risk-based scenarios for modernization.
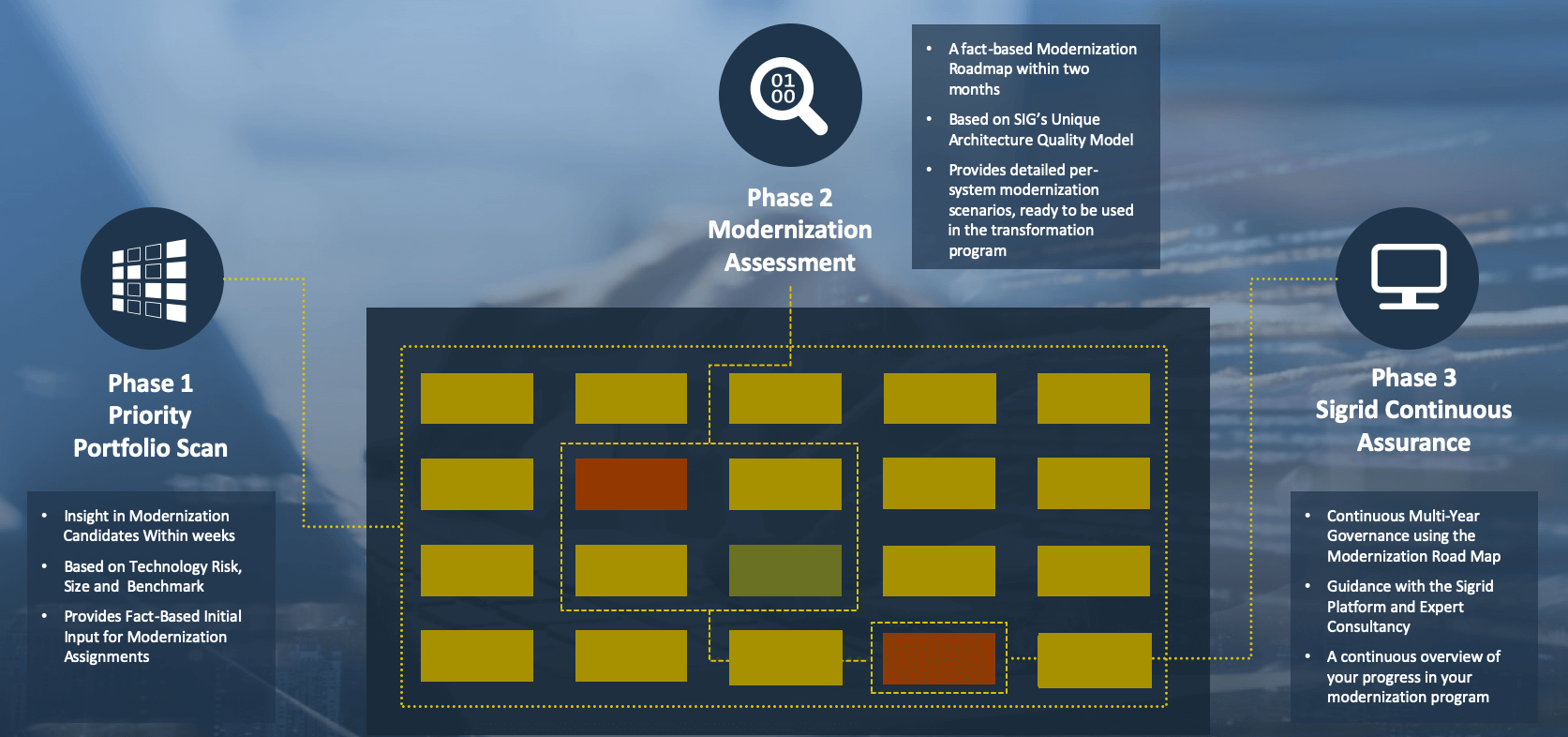
SIG Legacy Modernization Assurance comprises three phases:
Our Clients.
Who we help












Further reading
Swipe