
Software Improvement Group has been named a Leader in the 2026 Gartner® Magic Quadrant™ for Technical Debt Management Tools.
Software Improvement Group has been named a Leader in the 2026 Gartner® Magic Quadrant™ for Technical Debt Management Tools.
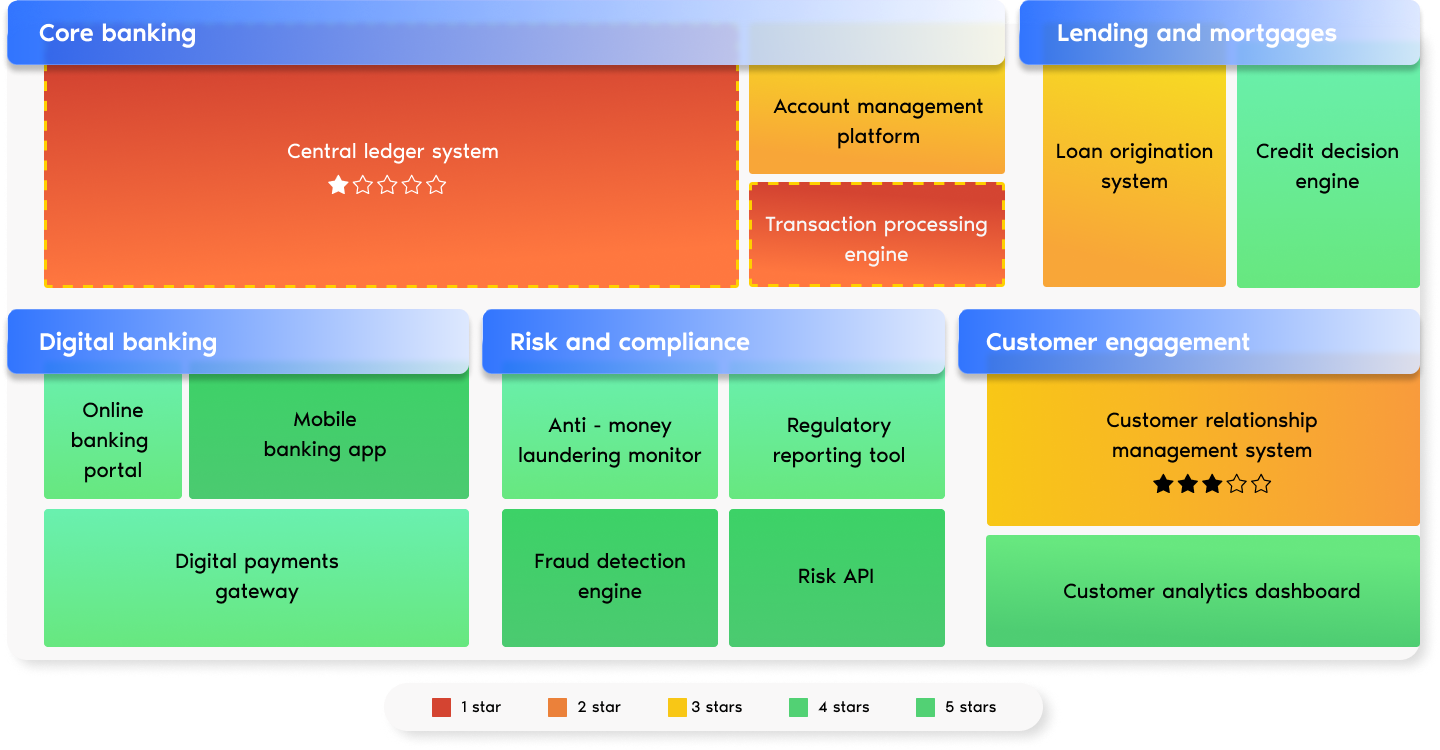
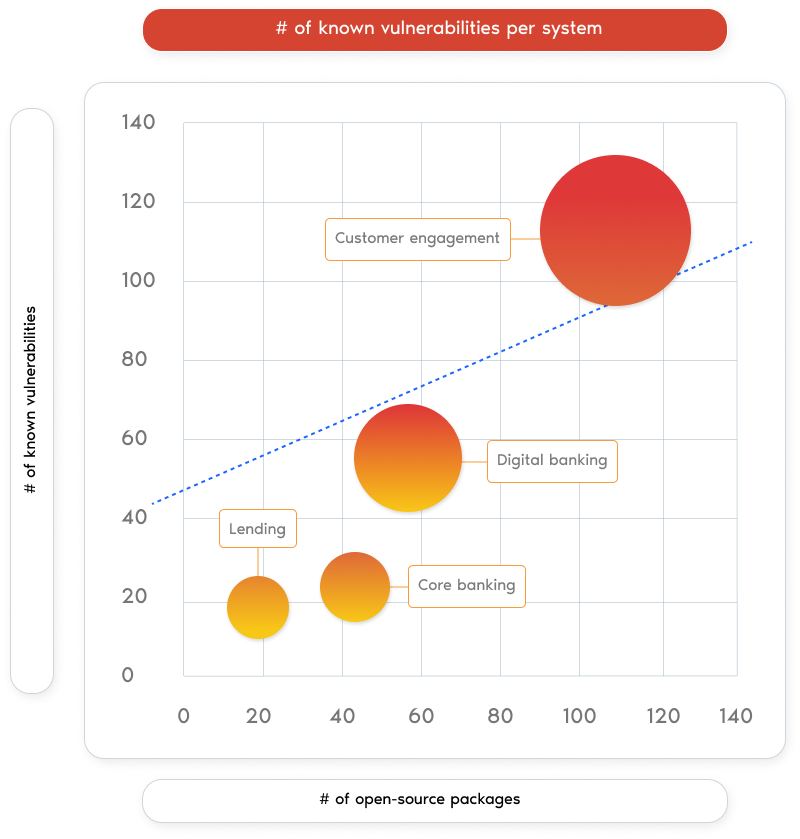
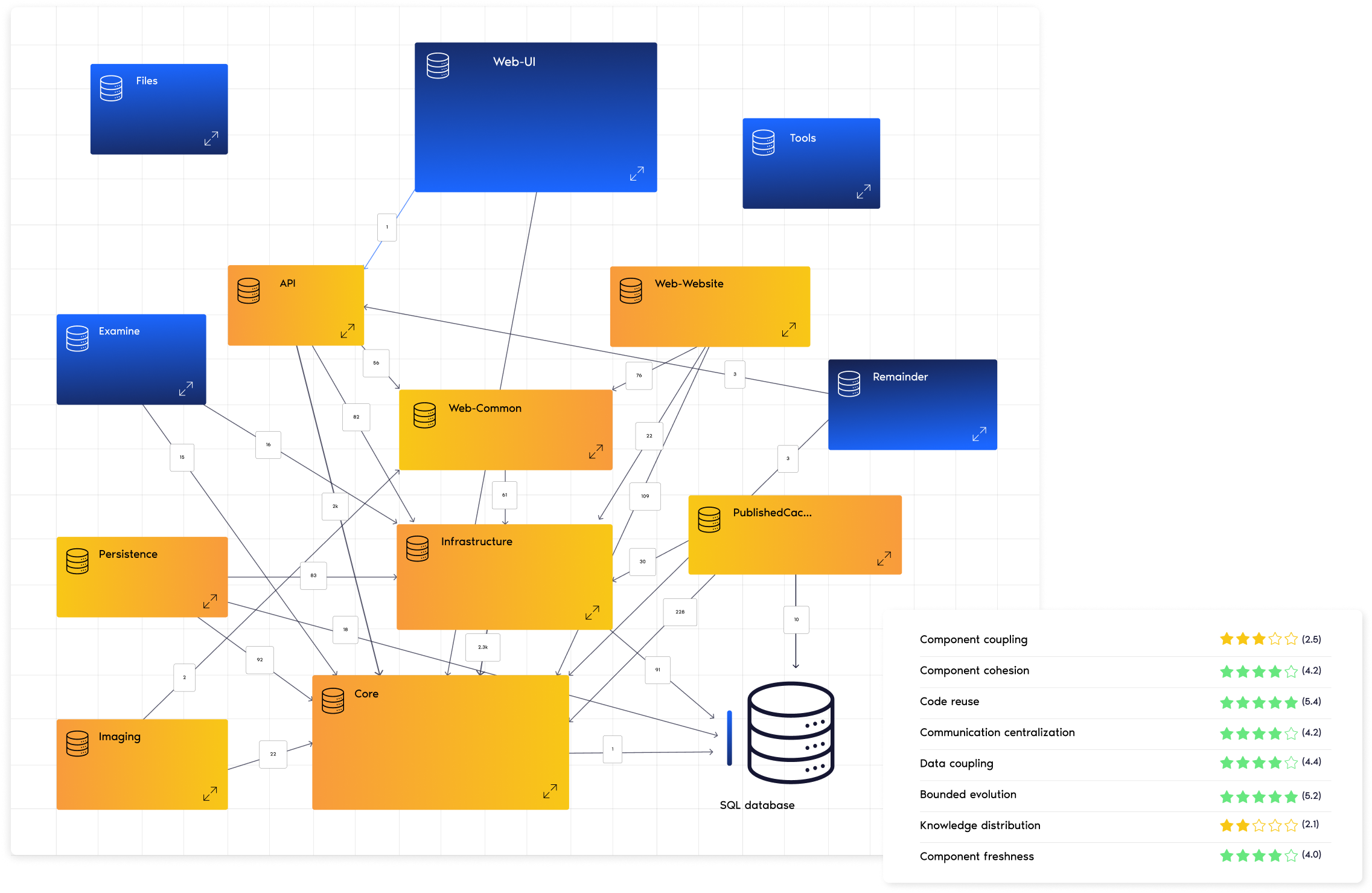
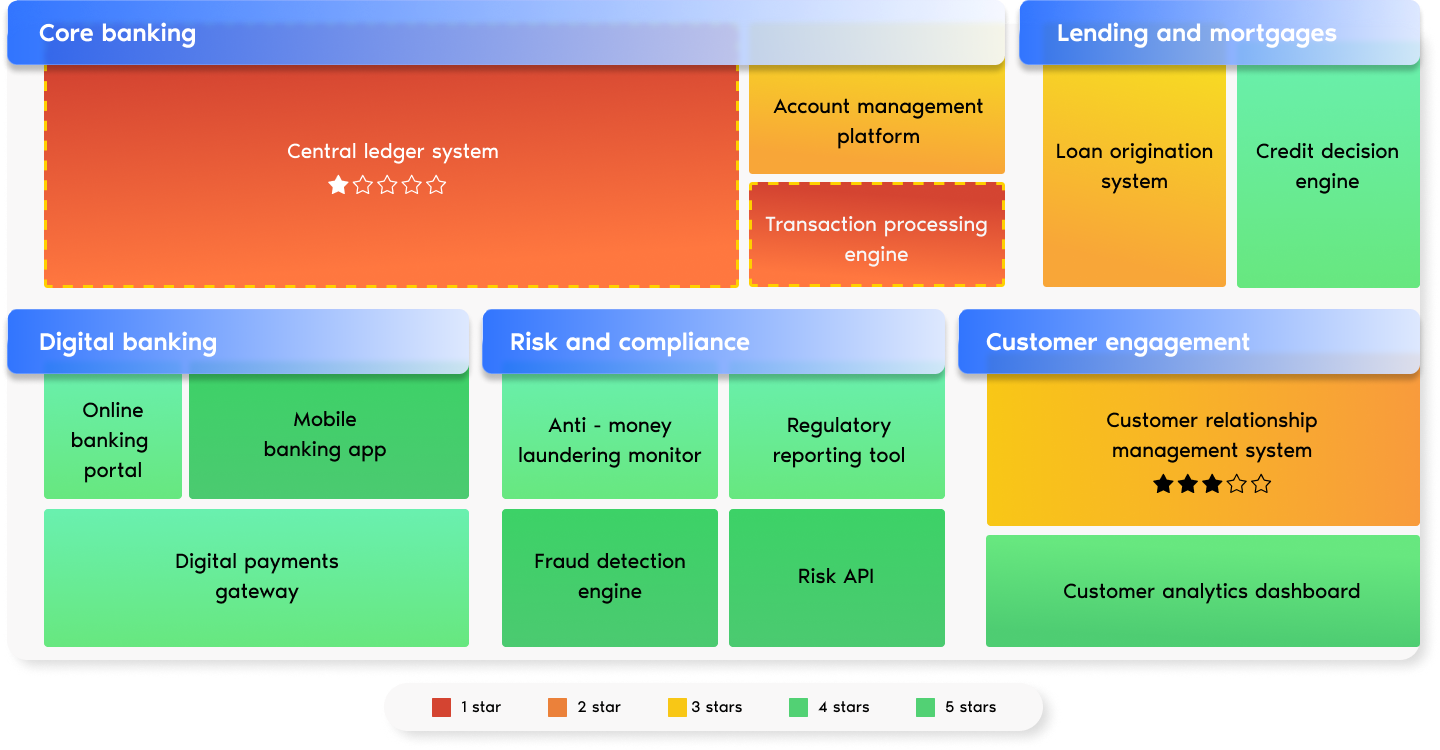
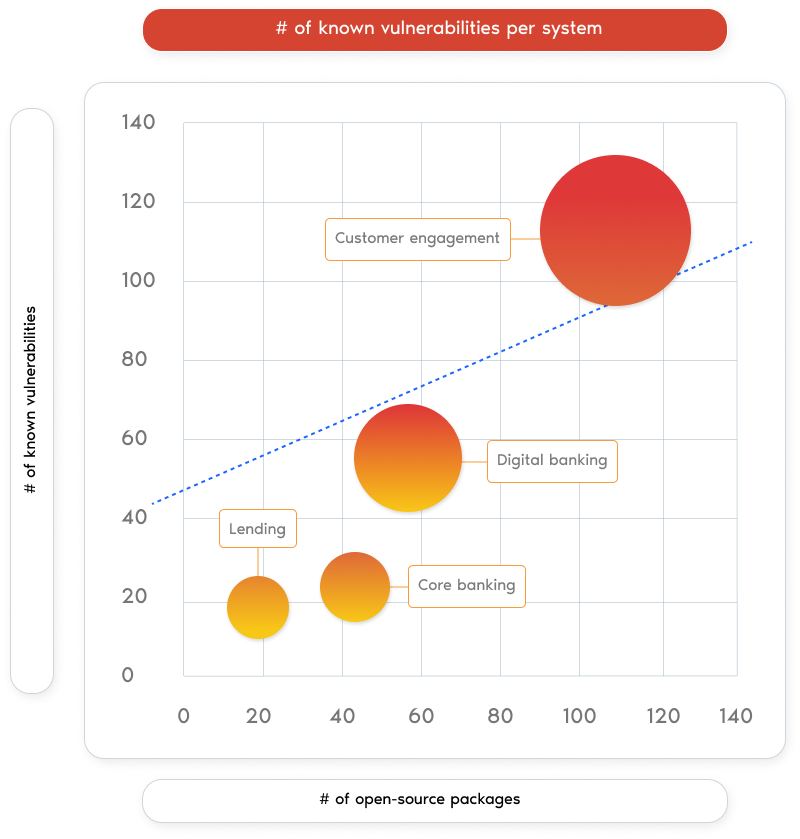
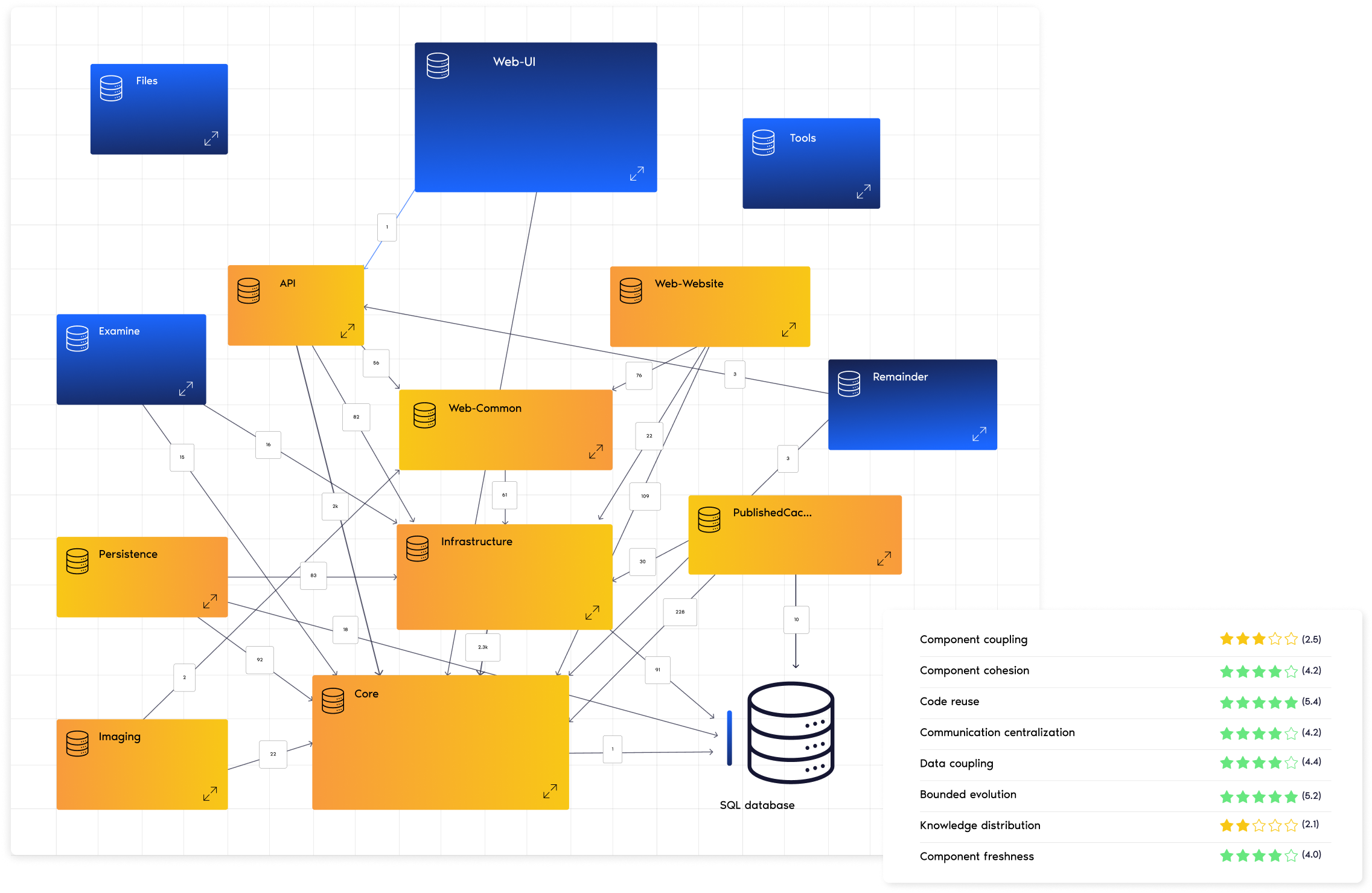
Software Portfolio Scan
Uncover inefficiencies, identify risks, and benchmark your software portfolio against the competition–In just two weeks.









of IT budgets are consumed by technical debt, making it a top challenge for CTOs (McKinsey).

is the average cost of a data breach, posing a major financial risk to any organization (IBM).

of organizations are struggling to implement AI at scale and achieve ROI (BCG)

is the surge in cyber insurance premiums, reflecting the financial impact of cyber threats (Insurance Journal)

Get fast, actionable recommendations on security, productivity, and architecture.

Know where you stand among industry peers. Are you ahead or behind competitors?

Gain actionable insights with minimal investment—no lengthy, expensive audits.

Receive a C-level-friendly report designed for executive buy-in and strategic decisions.

Reduce maintenance costs by 50% and speed up time-to-market up to 4x by tackling technical debt.

Deliver high-quality code with 15x fewer defects, 5x faster changes, and that's 2x more secure.





4.5X
FASTER TIME TO MARKET

-50%
LOWER MAINTENANCE COSTS

+30%
MORE DEVELOPMENT CAPACITY

2X
More SECURE software





Pinpoint risks, reduce costs, and future-proof your software portfolio