
24 July 2024
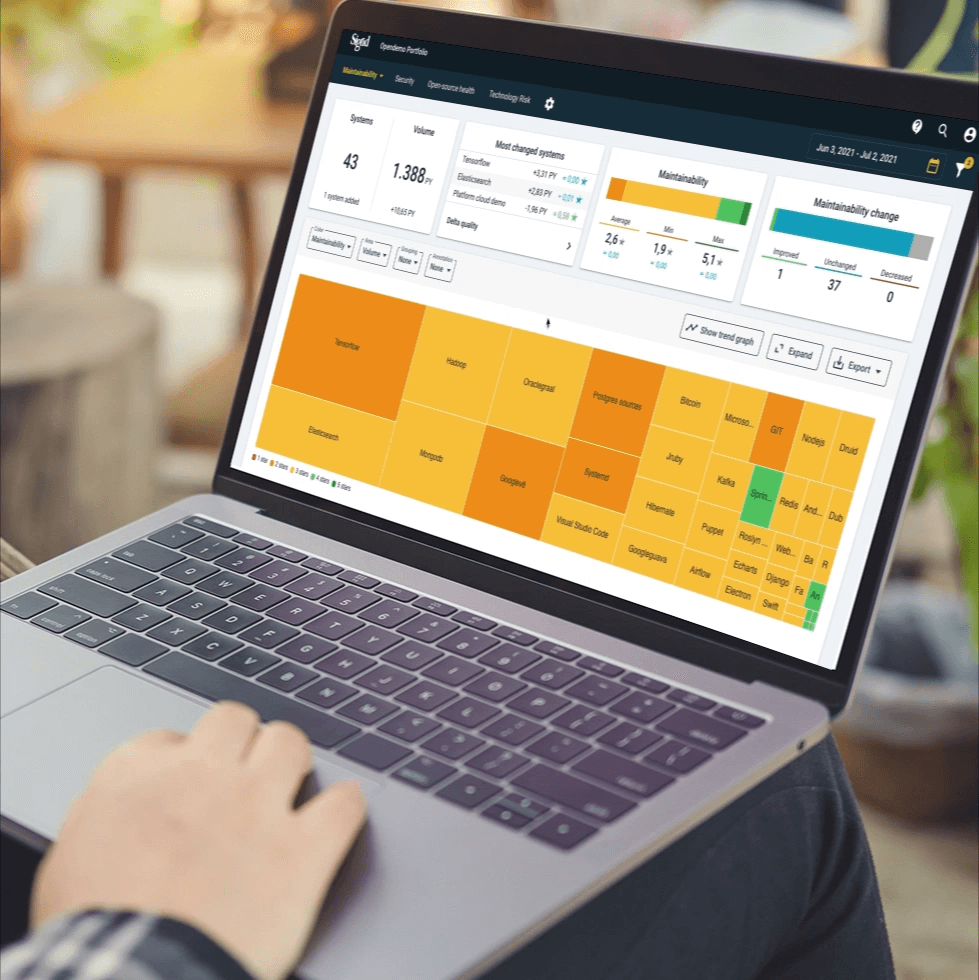
Request your demo of the Sigrid® | Software Assurance Platform:
2 min read
Written by: Haiyun Xu

A recent security vulnerability in Apache Log4j was identified on December 9th. The National Vulnerability Database published the relevant vulnerabilities in the following days, including CVE-2021-44228 with the highest severity score of 10. The vulnerabilities allow an attacker to run any arbitrary code through the Log4j Java library used for logging, or cause denial of service.
SIG immediately followed up with a detailed analysis of the SIG software systems for the CVE-2021-44228 vulnerability. We patched this in the Sigrid platform within 24 hours. The subsequent vulnerabilities, including but not limited to CVE-2021-45046 and CVE-2021-45105, were patched within hours.
Haiyun Xu, Chief Security Officer, stated,
“SIG secures software services with continuous and automated vulnerability detections. The team took immediate actions on high-risk vulnerabilities and maintained complete transparency with our clients regarding status updates. SIG immediately contacted impacted clients and supported them in securing their software systems.”
If you build and maintain your own software which uses log4j: To mitigate these vulnerabilities, update your system’s dependency to the latest version of log4j. Versions 2.16, 2.15 and older are not secure, but check https://logging.apache.org/log4j/2.x/security.html for the latest status. In circumstances where systems indirectly depend on log4j, package managers such as ‘Maven’ allow you to override the version used. If you cannot update log4j directly, follow Apache’s alternative instructions to mitigate the vulnerability: https://logging.apache.org/log4j/2.x/security.html
If you use software maintained by a vendor that contains log4j: Urge the vendor to release an update that contains a version of log4j without vulnerabilities (at least 2.17 at the time of writing), or mitigate the vulnerabilities in another way. Failing that, the Dutch NCSC has compiled a list of alternative mitigation measures you can use. It can be found at https://github.com/NCSC-NL/log4shell/tree/main/mitigation
If you don’t know whether software you use contains log4j: The Dutch NCSC has created an extensive list of software and whether it is vulnerable or not. They have also compiled a list of scan tools that can be used to identify log4j usage in software. Both can be found at https://github.com/NCSC-NL/log4shell
If you want to know whether these vulnerabilities were exploited in your infrastructure: The Dutch NCSC has compiled a list of methods you can use to “hunt” for evidence of exploitation: https://github.com/NCSC-NL/log4shell/tree/main/hunting
Additional sources of information regarding the vulnerabilities:
Author:
CISO, Head of Platform Team
We'll keep you posted on the latest news, events, and publications.