
24 July 2024
Request your demo of the Sigrid® | Software Assurance Platform:
8 min read

Developers are on high alert about a hugely popular open-source package. Node-ipc contains malicious code and has been downloaded millions of times. Earlier versions arbitrarily overwrite files with a heart emoji for users with an IP geolocated in Russia or Belarus.
Reported as “protestware” this vulnerability has been categorized with a severity score of “9.8 critical” by the National Vulnerability Database.
There has been a mixed response from the open-source community, some users were upset with the package maintainer actions and others expressed their support. RIAEvangelist (Brandon Nozaki Miller) was responsible for embedding the malicious code and has since replaced the code with an undesirable behavior that imports the peacenotwar package.
On the peacenotwar update, Brandon Miller commented, “This code serves as a non-destructive example of why controlling your node modules is important. It also serves as a non-violent protest against Russia’s aggression that threatens the world right now. This module will add a message of peace on your users’ desktops, and it will only do it if it does not already exist just to be polite.”
Pepijn van de Kamp, Head of Innovation at SIG, explains how we responded to the discovery of this vulnerability,
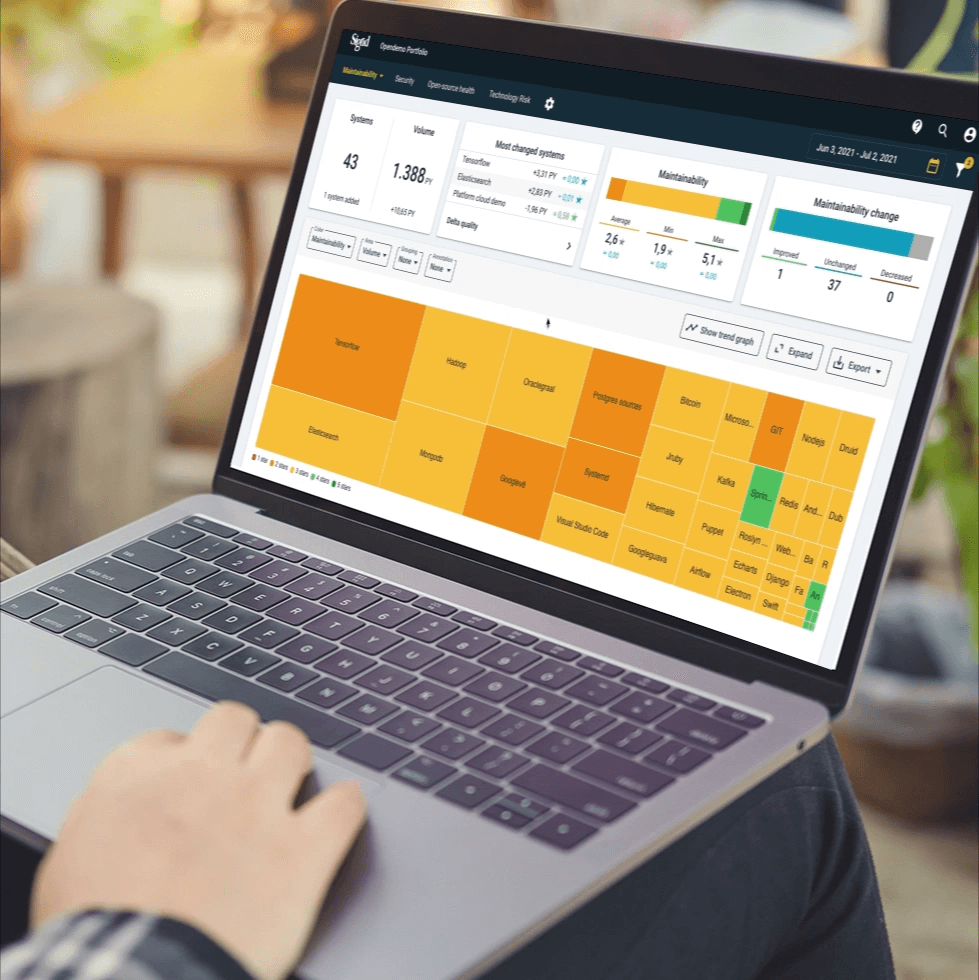
“As soon as the word got out on Github Security Advisories that yet another open-source maintainer inserted malicious code into a commonly used package, we used Sigrid® | Software Assurance platform to verify whether our internal and our client’s systems were affected. Using our open-source health module, which automatically indexes all used open-source components, we were able to quickly check for the presence of any publicly reported security issues and resolve them.”
Rob Van De Veer, Security Principal at SIG, commented,
“I see this incident as DEFCON 3 in the software supply chain challenge. DEFCON 5 is about developers making honest mistakes, say after some Champagne (Heartbleed). DEFCON 4 is when attackers gain access to source code (e.g. SolarWinds) and DEFCON 3 is when developers become the attackers.
Whether this attacker is morally right or not is beside the point. The safety and security of our digital world apparently depend on split decisions or little mistakes by individuals – right or wrong, intoxicated or perhaps having a bad day. The danger comes with the convenience of the modern-day software supply chain and it deserves attention that matches the risk, which means: a LOT of attention!
Proper secure software development is slowly catching on in organizations including the open-source world. As an industry, we’re taking steps, but slow ones. Slowly we are realizing the risks, slowly we are accepting that scanning tools will not find all weaknesses including the intentional ones. Slowly we are accepting that with all this affordable re-use it also comes with a responsibility that requires a budget.
In software security: there is no free lunch!”
If you would be interested in seeing a live demo of how we resolved security vulnerabilities and open-source risks using Sigrid® | Software Assurance platform exposes hidden risks and opportunities in your source code to assure full control over your application landscape. Get in touch to see a live demo.
About Node-ipc
Inter-Process Communication Module for node supporting Unix sockets, TCP, TLS, and UDP. Giving lightning speed on Linux, Mac, and Windows. A solution for complex multiprocess Neural Networking in Node.JS
References
We'll keep you posted on the latest news, events, and publications.